Health & Wellness
OT Safety Reimagined: From Legacy Limits to Community-Native Scale
Your OT safety proof-of-concept carried out flawlessly. Six months later, the enterprise-wide rollout has stalled. Budgets are exhausted, and demanding visibility gaps stay. If this sounds acquainted, you’re not alone.
Most industrial organizations uncover that OT safety options that work effectively in managed pilots change into unmanageable when deployed throughout a whole lot of switches, 1000’s of property, and a number of websites.
The stakes couldn’t be greater—with out complete visibility you can not successfully cut back the assault floor or implement community segmentation, and all it takes is a single compromised machine that may shut down complete manufacturing traces, costing thousands and thousands per hour.
The Hidden Price of Bolted-On Safety
Conventional OT visibility options depend on SPAN expertise to reflect community site visitors to devoted sensor home equipment. Whereas this method appears easy in a lab, it shortly turns into problematic at scale.
Contemplate a typical manufacturing plant with 100 or extra switches. Every change wants a sensor equipment to seize native site visitors, since most industrial communications occur on the cell layer between controllers. This east-west site visitors happens on the lowest ranges of the Purdue mannequin (Ranges 0-2) and doesn’t go by the standard north-south aggregation factors that join completely different zones to the commercial information middle. That’s 100+ home equipment to buy, deploy, energy, cool, and preserve. The capital and operational prices spiral uncontrolled.
Some distributors counsel utilizing Distant SPAN (RSPAN) to scale back equipment depend by forwarding site visitors from a number of switches to centralized sensors. This method backfires in manufacturing environments. RSPAN can double community site visitors, introducing jitter that disrupts time-sensitive industrial processes. In extremely automated amenities, this latency can sluggish manufacturing charges and break time synchronization between machines.
The choice—constructing an out-of-band SPAN assortment community—requires duplicating your complete community infrastructure. You want parallel switches, cabling, and upkeep assets. As your manufacturing community grows, so should this duplicated community. Many organizations abandon their deployments once they understand the true price.
Why Partial Visibility Equals No Safety
Even if you happen to can’t spend money on a visibility answer, you may suppose that lively discovery mechanisms will probably be enough for figuring out property. However Community Tackle Translation (NAT) will block these discovery requests.
Industrial gear producers standardize their machine configurations, reusing IP addresses throughout manufacturing cells. Whereas PLCs and HMIs may need translated addresses seen at Degree 3, the drives, security controllers, and I/O modules under stay hidden. In automotive manufacturing, for instance, 80% of Degree 0-2 gadgets sit behind NAT boundaries, invisible to centralized discovery instruments.
This visibility hole has critical penalties. You can not safe what you can not see. You can not section networks with out understanding communication patterns. And you can not adjust to laws like NERC CIP-15 or NIS2 with no full and updated asset stock.
Most critically, attackers exploit these blind spots. They transfer laterally by the invisible east-west site visitors between controllers, spreading ransomware or manipulating processes whereas defenders monitor the fallacious locations.
The Community-as-Sensor Revelation
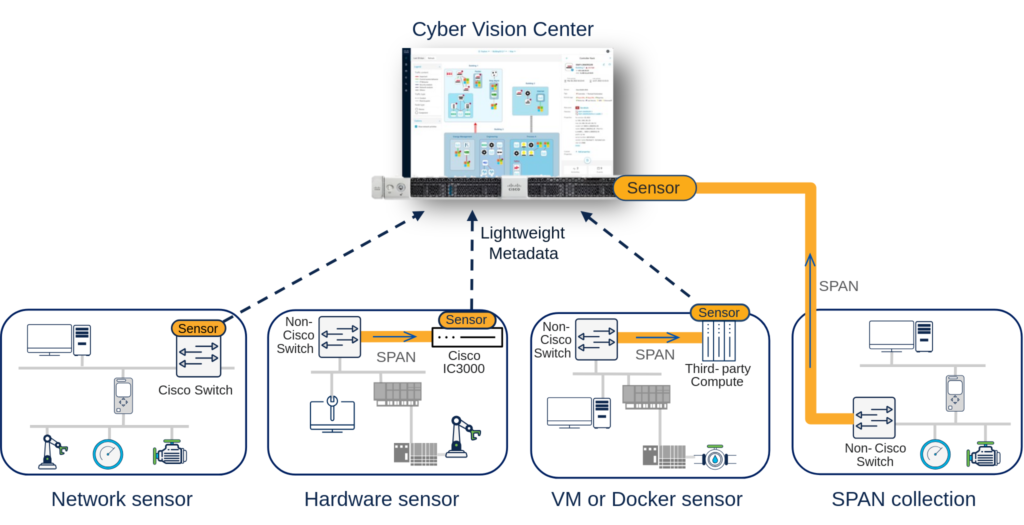
Cisco takes a essentially completely different method: as an alternative of bolting on safety home equipment, we embed visibility and safety capabilities straight into community infrastructure. Cisco Cyber Imaginative and prescient runs as software program inside industrial switches and routers, utilizing devoted CPU cores to carry out Deep Packet Inspection (DPI) with out impacting community efficiency. As a result of it operates on the edge the place gadgets join, it sees all site visitors and might actively question gadgets behind NAT boundaries.
Slightly than duplicating complete site visitors flows, Cyber Imaginative and prescient decodes IP and ICS protocols inside the change or router to extract solely the metadata it wants, including solely 2-5% site visitors to the community as an alternative of the 50-80% burden of conventional approaches. No extra home equipment. No SPAN assortment networks. No efficiency degradation.
For brownfield environments with non-Cisco gear, Cyber Imaginative and prescient deploys flexibly through Docker containers or digital machines. These sensors course of information domestically and don’t ahead packets. Provided that pricing relies on found endpoints and never variety of sensors deployed ends in seamless sensor deployment and scalability throughout brownfield environments.
Actual-World Community-Native Success
Complete visibility permits Zero Belief segmentation, important for holding breaches and sustaining operations throughout incidents. However segmentation with out full visibility is harmful—blocking official site visitors can shut down manufacturing.
Organizations deploying Cisco’s network-native method report speedy advantages past safety. Full visibility accelerates troubleshooting, decreasing imply time to restore. Automated asset stock simplifies regulatory audits. Having factual details about your OT safety posture additionally helps IT and OT groups collaborate to implement greatest practices.
Most significantly, this method scales. Whether or not you’re securing a single plant or a whole lot of web sites globally, the mannequin stays constant: now you can obtain complete industrial safety with out operational complexity.
Your Path Ahead
The selection is obvious. Bolted-on approaches to industrial safety lead to including operational complexity and price that also go away gaps. Merely acknowledged, this method isn’t constructed to scale. Conversely, Cisco’s method turns your community right into a safety sensor and enforcement mechanism, making extremely scalable industrial safety a actuality.
Begin by assessing your present visibility gaps and figuring out essential property. Consider options based mostly on scalability at manufacturing scale, not POC efficiency. Contemplate complete possession prices together with {hardware}, community capability, and operational overhead.
As industrial networks develop extra advanced and threats extra refined, the window for implementing efficient OT safety is narrowing. The query isn’t whether or not to safe your OT atmosphere, however whether or not you’ll select an method that really scales.
Able to be taught extra? Go to cisco.com/go/cybervision or meet the group on the S4x26 convention in Miami Feb 23-26, 2026.
Click on right here for the Answer Transient: Gaining Visibility into Industrial Networks at Scale